Published on:
10 min read
Remote Access Control Systems: 7 Trends Shaping Security
Remote access control has moved far beyond badge readers and a receptionist’s desk. Today’s systems combine cloud software, mobile credentials, video verification, identity management, and real-time analytics to help organizations secure doors, gates, elevators, and sensitive areas from anywhere. That shift matters because the threat landscape is changing quickly: hybrid work has multiplied credential risks, cyberattacks increasingly target physical security infrastructure, and multi-site operators need faster, more centralized control than legacy on-premise systems can provide. This article breaks down seven major trends shaping remote access control, including AI-driven monitoring, touchless entry, interoperability, and zero-trust security models. You’ll get specific examples, practical implementation advice, and a balanced view of where these systems deliver real ROI versus where they introduce complexity. Whether you manage an office portfolio, warehouse network, school campus, or multifamily property, the goal is simple: help you make smarter security decisions that reduce risk without creating friction for employees, residents, or visitors.

- •Why remote access control is becoming a core business system
- •Trend 1 and 2: Cloud-native platforms and mobile credentials are replacing legacy cards
- •Trend 3 and 4: Zero-trust principles and identity integration are reshaping physical security
- •Trend 5: AI, analytics, and remote video verification are turning events into decisions
- •Trend 6 and 7: Touchless entry, interoperability, and cybersecurity resilience are now expected
- •Key takeaways: how to choose and deploy a remote access control system wisely
- •Conclusion
Why remote access control is becoming a core business system
Remote access control used to be treated as a facilities expense. Now it sits much closer to cybersecurity, compliance, and operations. The reason is simple: when companies operate across multiple sites, support hybrid schedules, and onboard contractors constantly, door permissions become dynamic data, not static hardware. A modern administrator may need to unlock a server room in Chicago, revoke a vendor pass in Dallas, and review an after-hours entry event in London from one dashboard.
The market direction reflects that shift. Industry analysts have projected continued growth in cloud-based physical security, driven by demand for centralized management, lower maintenance overhead, and faster deployment. In practical terms, organizations are replacing isolated panels and local servers with web-managed systems that can sync users across directories, issue credentials remotely, and trigger alerts in real time.
Why it matters: physical access failures increasingly create business risk beyond theft. They can affect insurance claims, privacy obligations, employee safety, and even uptime if critical infrastructure rooms are compromised.
Common advantages include:
- Faster credential issuance for new hires and vendors
- Centralized audit trails for compliance reviews
- Lower dependence on on-site IT or locksmith visits
- Cloud reliance increases the importance of vendor uptime and network resilience
- Poorly configured role permissions can scale mistakes across many doors
- Subscription pricing may exceed legacy costs over several years if not managed carefully
Trend 1 and 2: Cloud-native platforms and mobile credentials are replacing legacy cards
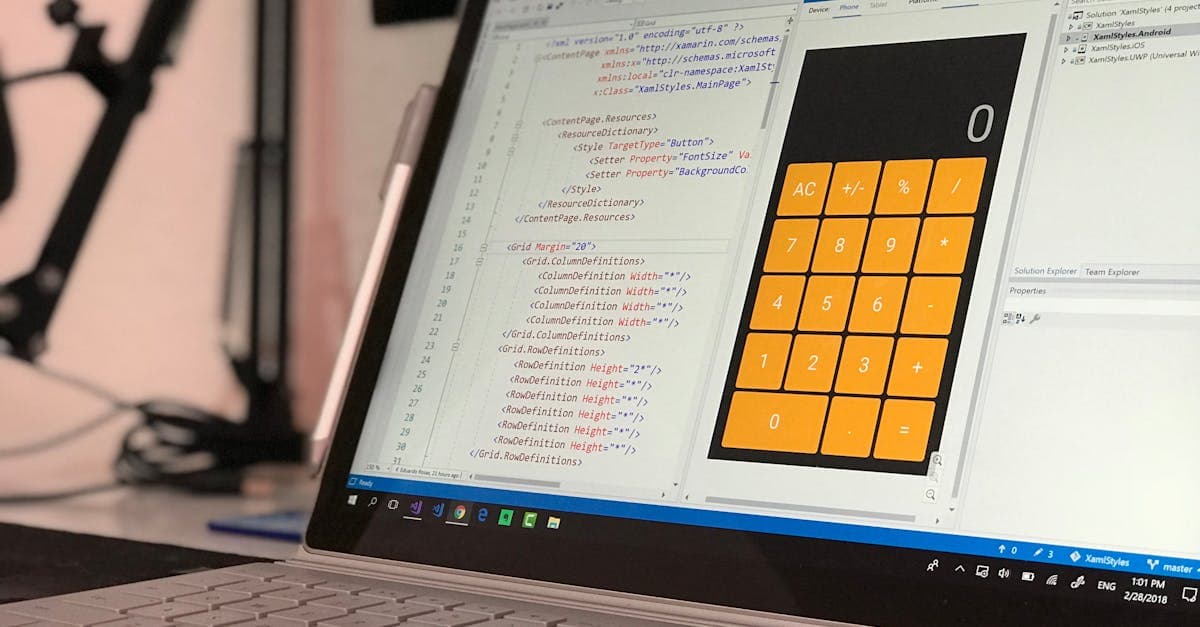
The first major trend is the migration from on-premise access control software to cloud-native platforms. Legacy systems often require VPN access, manual patching, local servers, and dealer intervention for even minor changes. Cloud-first platforms reduce that friction by allowing administrators to add users, change schedules, or monitor doors through a browser or app. For a regional property manager with 25 buildings, that can cut response time from hours to minutes.
The second trend is the rapid adoption of mobile credentials. Instead of printing and replacing plastic cards, organizations issue secure credentials to smartphones using Bluetooth Low Energy, NFC, or wallet-based passes. Universities have been early adopters because students already live on their phones, but the same model is spreading across offices, healthcare clinics, and multifamily communities.
A real-world scenario illustrates the appeal: when a contractor loses a physical badge, replacement may require in-person verification and card programming. With mobile credentials, access can be revoked instantly and reissued remotely after identity confirmation.
Benefits of mobile-first access include:
- Lower card printing and replacement costs
- Faster remote provisioning for temporary users
- Better user convenience, especially for shared offices
- Battery dependence and phone loss scenarios
- Privacy concerns if users feel location data is being over-collected
- Compatibility issues with older readers and mixed hardware estates
Trend 3 and 4: Zero-trust principles and identity integration are reshaping physical security
One of the most important shifts in access control is the application of zero-trust thinking to physical spaces. In cybersecurity, zero trust means never assuming a user or device is trustworthy by default. In access control, that translates into least-privilege permissions, continuous verification, tighter schedules, and stronger event correlation. Instead of giving broad all-day building access to large groups, organizations are creating narrower roles based on job function, site, and time window.
This trend connects directly to identity integration. Modern systems increasingly sync with HR platforms, identity providers, and directories such as Microsoft Entra ID or Okta. When an employee changes departments or leaves the company, access rights can update automatically instead of relying on a help desk ticket someone might miss. That matters because former employee misuse remains a real concern, especially in industries with valuable inventory, research assets, or resident data.
A useful example comes from healthcare and life sciences environments. A researcher may need lab access only during approved project windows and only after completing training. Integrated systems can verify that status before assigning permissions, reducing administrative gaps.
Pros of identity-led access control:
- Faster onboarding and cleaner offboarding
- Reduced orphaned credentials and stale permissions
- Stronger auditability for compliance-driven sectors
- Integration projects can become complex across older systems
- Bad source data from HR or directory tools can spread errors quickly
- Overly rigid rules may frustrate staff who need occasional exceptions
Trend 5: AI, analytics, and remote video verification are turning events into decisions
Access control logs have always generated data, but most organizations historically used that data only after an incident. The next trend is operationalizing it in real time through AI-assisted analytics and remote video verification. Instead of simply recording that Door 14 opened at 2:13 a.m., a modern system can correlate the event with camera footage, unusual schedule behavior, and anti-passback anomalies, then escalate it to a remote guard or security manager.
This matters because false alarms are expensive. In many cities, repeated false dispatches can trigger fines or strain law enforcement relationships. Video verification helps teams determine whether an event is a tailgating attempt, a delivery issue, or a legitimate employee arrival. For smaller businesses that cannot staff a 24-hour security desk, that extra context is especially valuable.
AI is also being used to spot patterns humans miss. Examples include repeated failed access attempts across multiple sites, unusual door-held-open durations, or occupancy trends that suggest a policy mismatch. A logistics company, for instance, might discover that after-hours entries spike every quarter-end because supervisors are sharing credentials informally to speed shipping deadlines.
The upside is compelling:
- Faster incident triage and fewer blind alarm responses
- Better forensic review with synchronized video and access events
- More useful reporting for compliance and operational planning
- AI systems can produce false positives if camera placement or training data is weak
- Storage and bandwidth costs can rise quickly with video-heavy deployments
- Privacy and labor-law concerns require transparent policies and retention limits
Trend 6 and 7: Touchless entry, interoperability, and cybersecurity resilience are now expected
Touchless entry accelerated during the pandemic, but it has stayed for reasons that go beyond hygiene. Employees and residents prefer faster, frictionless access, especially in high-traffic environments such as apartment lobbies, hospitals, and corporate campuses. Wave-to-open sensors, mobile unlock, facial recognition in limited use cases, and visitor QR codes all reduce bottlenecks. In office settings, even saving five seconds per entry can matter when hundreds of people arrive during the same 20-minute window.
At the same time, buyers now expect interoperability. They want access control to work with video, intrusion detection, visitor management, elevator controls, and building automation rather than operating as a silo. This is where open APIs and standards-based integrations matter. A practical example: if a terminated employee’s access is revoked, the same workflow may also disable their visitor pre-registration privileges and trigger an alert if their credential is presented again.
The final trend is cybersecurity resilience. Physical security devices are networked endpoints, which means readers, controllers, and management consoles can become attack surfaces. Recent years have seen increased scrutiny on default passwords, unencrypted traffic, unsupported firmware, and insecure remote admin tools.
What strong buyers now require:
- Encrypted communication between controllers, readers, and cloud services
- Role-based admin controls with multifactor authentication
- Firmware update policies and documented vulnerability response timelines
- More integrations can mean more failure points during deployment
- Advanced touchless features may raise consent and bias concerns, especially with biometrics
- Strong cyber hardening can increase implementation time and procurement complexity
Key takeaways: how to choose and deploy a remote access control system wisely
If you are evaluating or upgrading a remote access control system, start with risk, not features. List the spaces that truly matter: server rooms, medicine storage, loading docks, executive suites, resident amenities, or child pickup areas. Then map who needs access, when, and under what conditions. That exercise prevents a common mistake: buying sophisticated software but keeping overly broad permissions that weaken the entire investment.
A practical selection checklist should include a few non-negotiables. Ask vendors how they handle credential revocation latency, audit log retention, cybersecurity patching, and offline door behavior during internet outages. Request customer references in your exact environment, because a school, warehouse, and multifamily building have very different workflows. If possible, pilot the system at one site for 60 to 90 days before full rollout.
Implementation tips that consistently pay off:
- Connect HR or identity systems early so onboarding and offboarding are automated
- Define clear visitor, contractor, and after-hours approval policies before launch
- Train managers on exception handling so they do not create unsafe workarounds
- Review access groups quarterly and remove inherited permissions that no longer fit
- Test emergency lockdown, unlock, and fail-safe behavior under realistic conditions
Conclusion
Remote access control is no longer just about opening doors remotely. The biggest trends shaping the market, from cloud management and mobile credentials to zero-trust policies, AI-assisted monitoring, touchless entry, interoperability, and cyber resilience, all point to one reality: physical security is becoming data-driven and deeply connected to business operations. The smartest next step is to audit your current access model, identify high-risk gaps, and prioritize improvements that reduce both friction and exposure. Start small if needed, but be deliberate. Choose a platform that can integrate cleanly, enforce strong identity controls, and scale without multiplying administrative burden. In security, convenience gets attention, but disciplined governance is what delivers long-term protection.
Published on .
Share now!
HM
Henry Mason
Author
The information on this site is of a general nature only and is not intended to address the specific circumstances of any particular individual or entity. It is not intended or implied to be a substitute for professional advice.